Why Manufacturing Is The Biggest Target For Ransomware Attacks
Data security in the manufacturing industry isn’t always held to the higher standards of industries like finance or ...
Data security in the manufacturing industry isn’t always held to the higher standards of industries like finance or insurance, but the potential damage of a breach can be just as serious.
A recent report by IBM revealed manufacturing organizations were the most frequent target of ransomware attacks of the past year as cybercriminals attempted to disrupt global supply chains.
“Threat actors understand the critical role manufacturing and energy play in global supply chains and are seeking to disrupt these organizations because of the ripple effect it can have across multiple industries and the pressure these multiplying effects create for victims to pay a ransom,” the report states.
While the financial and insurance sectors have been the most common targets of cyber threats in previous years, this finding reflects a change in ransomware tactics and the ways in which attackers exploit sensitive data.
Recent ransomware attacks in manufacturing
As cyber risks accelerated and ransomware gangs like REvil, Conti and Lockbit became more aggressive, many manufacturing companies have felt the impact. Toyota recently announced it was suspending 28 production lines at 14 factories following a cyberattack. Make UK reported half of all British manufacturers — including 62% of automakers — experienced a successful cyberattack in the past year, according to Info Security Magazine.
In other high-profile attacks, the Babuk ransomware group reportedly stole personally identifiable information data from power tool manufacturer Yamabiki, among other targets, and published it to a data leak site.
And Brenntag, a chemical distribution company, paid $4.4 million in ransom to decrypt its encrypted data, which included Social Security numbers.
The most common causes of ransomware attacks on manufacturing companies
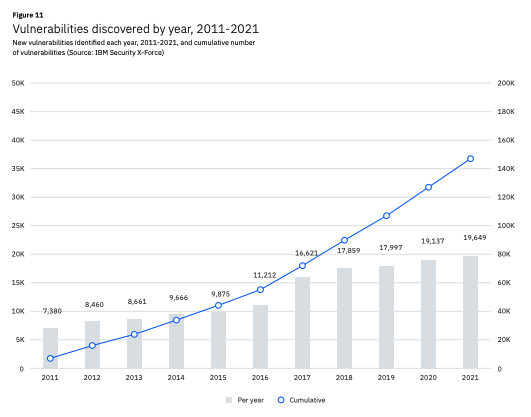
In addition to phishing schemes, ransomware attackers have been using a growing number of common vulnerabilities and exposures (CVEs) to gain access to manufacturing company networks, according to the IBM report.
 Many of these vulnerabilities are related to digital technologies connected to the Internet of Things and industrial control systems. One specific target is a port that uses Modbus to provide communication between connected buses, networks and programmable logic controller devices in industrial networks, according to the report.
Many of these vulnerabilities are related to digital technologies connected to the Internet of Things and industrial control systems. One specific target is a port that uses Modbus to provide communication between connected buses, networks and programmable logic controller devices in industrial networks, according to the report.
Gaining access to Modbus can allow threat actors to control any equipment connected to the internet.
IBM notes 47% of attacks on manufacturing were caused by vulnerabilities companies had not found or had not addressed as the attack surface extends to the cloud.
How to improve data security in the manufacturing industry
While the manufacturing industry has made significant advances in digital transformation, many organizations are still catching up when it comes to cybersecurity maturity.
A 2019 Deloitte report found that while 90% of manufacturers had the capabilities to detect cyber attacks, very few were monitoring their operational technology environments. Fewer than half had performed a cybersecurity assessment in the past six months.
As we’ve seen in recent ransomware attacks, focusing only on common attack vectors and perimeter security measures is no longer enough. Manufacturers need to acknowledge the significant data security threats they face from ransomware attackers as well as within their own organization. In addition to disrupting operations, attackers can steal intellectual property, such as product designs or manufacturing processes.
“Instead of operating under the assumption that every vulnerability in their environment has been patched, businesses should operate under an assumption of compromise, and enhance their vulnerability management with a zero trust strategy,” said Charles Henderson, Head of IBM X-Force.
Myota’s Converged Data Security platform combines the principles of zero trust architecture, data encryption, immutable redundant storage and advanced data dispersion. This enables manufacturers to withstand ransomware attacks without experiencing data theft or downtime due to data loss. The way data is encrypted and dispersed prevents attackers from being able to use it while making it easy for policy administrators to restore data if needed.
Myota protects your data across storage locations, allowing administrators to have full control over locations, users and devices. For employees, it’s as easy as saving sensitive documents to a new location.
Learn more about how Myota improves data protection in the manufacturing industry.


